In today’s cloud-centric world, ensuring the security and privacy of your data is paramount. While cloud providers offer robust encryption options, many organizations are seeking greater control over their data protection strategies. This is where Bring Your Own Key (BYOK) encryption comes into play. BYOK is a crucial capability that empowers you to manage your own encryption keys, even when your data resides in the cloud. This article, “BYOK Encryption Explained: Taking Control of Your Data Security in the Cloud,” provides a comprehensive overview of BYOK, its benefits, implementation considerations, and how it strengthens your overall security posture.
This article delves into the intricacies of BYOK encryption, exploring how it differs from other encryption methods offered by cloud service providers (CSPs). We’ll examine the advantages of maintaining control over your encryption keys, including enhanced compliance with industry regulations, improved data sovereignty, and greater flexibility in managing access controls. Furthermore, we’ll discuss the technical aspects of BYOK, including key generation, storage, and lifecycle management, providing a practical guide for organizations looking to implement this powerful security solution to bolster their cloud data security.
What is BYOK (Bring Your Own Key) Encryption and How Does It Work?
BYOK, or Bring Your Own Key, is an encryption method where organizations generate and manage their own encryption keys used to protect data stored in a third-party environment, such as a cloud service. This differs from standard cloud encryption where the cloud provider manages the keys.
The process generally involves these steps:
- Key Generation: The organization creates encryption keys using their own hardware or software, often within a Hardware Security Module (HSM).
- Key Import: The generated key is securely transferred to the cloud provider’s key management system.
- Data Encryption: Data is encrypted using the imported key before or during its storage in the cloud.
- Key Management: The organization retains control over the lifecycle of the key, including rotation, revocation, and destruction.
By maintaining control of the encryption keys, organizations gain greater visibility and control over their data security posture, as well as ensuring the cloud provider cannot decrypt their data without their explicit consent.
The Benefits of Using BYOK Encryption for Data Security
Implementing Bring Your Own Key (BYOK) encryption offers several distinct advantages for enhancing data security within cloud environments. Foremost among these is enhanced control over encryption keys. Unlike provider-managed encryption, BYOK allows organizations to maintain sole custody of their cryptographic keys, minimizing the risk of unauthorized access by the cloud provider or other third parties.
Another key benefit is improved compliance posture. BYOK can assist organizations in meeting stringent regulatory requirements, particularly those pertaining to data residency, data sovereignty, and data access controls. By retaining control over the encryption keys, companies can demonstrate their commitment to protecting sensitive data in accordance with applicable laws and industry standards.
Furthermore, BYOK provides increased transparency and auditability. Organizations can independently monitor and audit key usage, ensuring that data is protected according to their own security policies. This level of control can be crucial for maintaining trust and accountability in cloud environments.
Finally, BYOK can contribute to a stronger overall security posture by reducing reliance on the cloud provider’s security infrastructure. While cloud providers invest heavily in security, BYOK adds an extra layer of protection by giving organizations direct control over the encryption keys that protect their data.
BYOK vs. Other Encryption Methods: A Comparative Analysis
BYOK (Bring Your Own Key) encryption offers a unique approach to data security compared to other common encryption methods. Understanding these differences is crucial for choosing the right strategy.
Here’s a brief comparison:
- Cloud Provider-Managed Encryption: The cloud provider generates and manages the encryption keys. This is the simplest approach but gives you the least control. With BYOK, you maintain control.
- Hardware Security Modules (HSMs): HSMs provide a secure, dedicated hardware environment for key storage and cryptographic operations. BYOK often utilizes HSMs for enhanced security.
- Client-Side Encryption: Data is encrypted before being uploaded to the cloud. This gives you maximum control but can be complex to implement and manage. BYOK offers a middle ground, leveraging cloud services while retaining key control.
The primary advantage of BYOK lies in its balance between control and convenience. You maintain ownership of your encryption keys, allowing for greater regulatory compliance and peace of mind. Other methods may offer simplicity or complete control, but BYOK provides a strong compromise for many organizations.
When Should You Consider Using BYOK Encryption?
BYOK (Bring Your Own Key) encryption is not a one-size-fits-all solution. It is most beneficial when your organization has specific security and compliance requirements that cannot be met by the default encryption options offered by cloud providers.
Consider implementing BYOK when:
- You require granular control over your encryption keys and their lifecycle.
- You need to meet strict regulatory mandates, such as HIPAA, GDPR, or PCI DSS, that demand independent key management.
- You operate in a highly sensitive industry, like finance or healthcare, where data breaches can have severe consequences.
- You want to minimize the risk of vendor lock-in by maintaining control over your encryption keys.
- Your organization has a mature key management infrastructure and expertise.
In essence, if maintaining independent control and visibility over your encryption keys is a critical business requirement, then BYOK should be seriously considered.
Key Considerations Before Implementing BYOK Encryption
Before embarking on a Bring Your Own Key (BYOK) encryption strategy, organizations must carefully evaluate several crucial factors. A thorough understanding of these considerations will contribute to a successful and secure implementation.
Key Management Infrastructure: Establishing a robust and secure key management system is paramount. This includes considering hardware security modules (HSMs) for key storage and implementing strict access controls. The lifecycle management of keys, from generation to rotation and destruction, should be clearly defined and meticulously followed.
Compatibility and Integration: Ensure that the chosen BYOK solution is compatible with your existing cloud services, applications, and infrastructure. A comprehensive assessment of integration complexities is necessary to avoid unforeseen issues and potential disruptions to workflows.
Operational Overhead: BYOK introduces additional operational responsibilities. Teams need to be trained in key management best practices, and processes must be established for monitoring, auditing, and incident response. Account for the increased administrative burden and allocate resources accordingly.
Cost Analysis: While BYOK offers enhanced control, it can also introduce new costs associated with key management infrastructure, licensing, and personnel. Conduct a thorough cost-benefit analysis to determine the overall financial impact of implementing BYOK.
How to Generate and Manage Your Encryption Keys
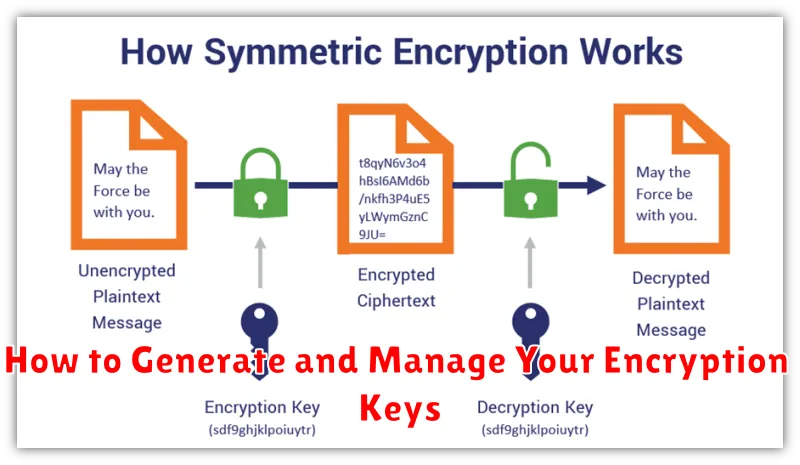
The generation and management of encryption keys are paramount to the security of a BYOK (Bring Your Own Key) system. Strong, randomly generated keys are essential for robust encryption. Several methods exist for key generation, including using hardware security modules (HSMs) or software-based cryptographic libraries.
Once generated, secure key storage is crucial. Options include HSMs, secure enclaves, or carefully managed key vaults. Access controls must be strictly enforced to prevent unauthorized access or modification.
A robust key management lifecycle should be implemented, encompassing key rotation, backup, and recovery procedures. Regular key rotation minimizes the impact of potential key compromises. Secure backups ensure data can be recovered in case of key loss or corruption. Well-defined recovery procedures are vital for restoring access to encrypted data following unforeseen events. A central key management system is often required to perform these operations effectively.
Integrating BYOK Encryption with Cloud Services and Applications
Integrating BYOK encryption with cloud services and applications requires careful planning and execution. The core process involves securely transferring your encryption keys to the cloud provider’s environment, often using Hardware Security Modules (HSMs) or similar secure key management solutions.
Many cloud providers offer specific APIs and tools to facilitate BYOK integration. These tools allow you to register your keys with the cloud service and configure the encryption settings for your data at rest and in transit. Before integrating, it’s crucial to verify that the cloud provider supports the specific key management standards and encryption algorithms you require.
When integrating BYOK with applications, ensure that the application is designed to utilize the encryption keys provided by the cloud service. This may involve modifying the application’s code or configuration to point to the correct key management endpoints and encryption libraries. Proper testing and validation are essential to guarantee that the encryption is functioning correctly and that data is adequately protected.
Compliance and Regulatory Requirements for BYOK Encryption
BYOK encryption is increasingly important for meeting various compliance and regulatory requirements. Organizations handling sensitive data, especially in regulated industries such as healthcare (HIPAA), finance (PCI DSS, GDPR), and government, must adhere to specific data protection standards.
BYOK allows organizations to maintain control over their encryption keys, which can be a crucial factor in demonstrating compliance. For example, certain regulations mandate that data controllers have exclusive control over the keys used to encrypt personal data. BYOK enables this level of control, assisting in meeting such requirements.
Specifically, compliance with regulations like GDPR’s Article 32 (Security of processing), which requires appropriate technical and organizational measures to ensure a level of security appropriate to the risk, can be supported by BYOK. Similarly, HIPAA’s Security Rule necessitates encryption of protected health information (PHI) at rest and in transit, and BYOK offers a means to manage the encryption keys in accordance with organizational policies.
Potential Challenges and Mitigation Strategies for BYOK Encryption
Implementing BYOK encryption presents several potential challenges. One primary concern is the increased complexity of key management. Losing control of your encryption keys can lead to permanent data loss. To mitigate this, organizations should implement robust key management systems with strong access controls and regular backups. Consider using Hardware Security Modules (HSMs) for secure key storage.
Another challenge involves the potential for performance overhead. Encrypting and decrypting data using your own keys can add latency, particularly for frequently accessed data. Mitigation strategies include optimizing encryption algorithms and leveraging caching mechanisms. Thorough performance testing is crucial before deploying BYOK.
Furthermore, ensuring compatibility with existing cloud services and applications can be complex. Not all services seamlessly integrate with BYOK. A comprehensive compatibility assessment should be performed, and alternative solutions may need to be considered for incompatible systems. Standardized key formats and APIs can help improve interoperability.
Finally, consider the ongoing administrative burden. Maintaining key security, ensuring compliance, and responding to security incidents requires dedicated resources and expertise. Automate key rotation and monitoring processes where possible and provide adequate training for IT staff.
The Future of BYOK Encryption and Its Impact on Cloud Security
The future of BYOK (Bring Your Own Key) encryption is inextricably linked to the evolving landscape of cloud security. As organizations increasingly adopt multi-cloud and hybrid cloud strategies, the need for granular control over encryption keys becomes paramount.
We anticipate a greater emphasis on automation and simplification in key management processes, making BYOK more accessible to a wider range of businesses. Expect to see advancements in key rotation, auditing, and revocation capabilities.
Quantum-resistant cryptography will likely play a significant role in the future of BYOK, mitigating the threat posed by quantum computing to current encryption algorithms. Furthermore, the integration of hardware security modules (HSMs) and secure enclaves will further enhance the security posture of BYOK implementations.
Ultimately, BYOK will empower organizations to maintain data sovereignty and meet increasingly stringent regulatory requirements in a cloud-first world.