In today’s complex digital landscape, securing applications and ensuring seamless user access is paramount. Organizations face a crucial decision when choosing an authentication protocol for managing user identities and controlling access to their valuable resources. Two prominent solutions stand out: Security Assertion Markup Language (SAML) and OpenID Connect (OIDC). This article provides a comprehensive comparison of SAML Authentication vs. OpenID Connect, delving into their respective strengths, weaknesses, and ideal use cases. Understanding the nuances of each protocol is essential for making informed decisions that align with your organization’s specific security and functionality requirements. We will explore how each handles identity federation, single sign-on (SSO), and the exchange of authentication and authorization data.
This in-depth analysis will equip you with the knowledge to strategically select the optimal authentication method for your applications. We will dissect the technical intricacies of both SAML and OpenID Connect, including their underlying architectures, data formats, and security considerations. We will also explore real-world scenarios where each protocol shines, helping you understand when to leverage SAML for enterprise-grade identity management and when OpenID Connect’s modern, API-friendly approach is the better fit. By the end of this comparison, you will have a clear understanding of which protocol best suits your organization’s needs for secure and efficient user authentication.
Understanding SAML Authentication: A Detailed Overview
SAML (Security Assertion Markup Language) is an open standard for exchanging authentication and authorization data between security domains, specifically between an Identity Provider (IdP) and a Service Provider (SP). It enables single sign-on (SSO), allowing users to access multiple applications with a single set of credentials.
At its core, SAML operates through XML-based messages. The IdP authenticates the user and then passes an SAML assertion, which is a digitally signed XML document, to the SP. This assertion contains information about the user’s identity and attributes.
Key Components of SAML Authentication:
- Principal: The user being authenticated.
- Identity Provider (IdP): The system that authenticates the user and issues SAML assertions.
- Service Provider (SP): The application or service that the user wants to access.
- Assertion: An XML document containing statements about the user.
The process generally involves the user attempting to access a service on the SP. The SP redirects the user to the IdP for authentication. Upon successful authentication, the IdP sends the SAML assertion back to the SP, granting the user access.
Exploring OpenID Connect: How It Works and Key Features
OpenID Connect (OIDC) is an authentication protocol built on top of the OAuth 2.0 authorization framework. It allows clients to verify the identity of the end-user based on the authentication performed by an Authorization Server, as well as to obtain basic profile information about the end-user in an interoperable and REST-like manner.
Key Features of OpenID Connect:
- Single Sign-On (SSO): Enables users to access multiple applications with a single set of credentials.
- Standardized Protocol: Provides a well-defined and widely adopted standard for identity verification.
- RESTful API: Utilizes RESTful APIs for communication, making it easier to integrate with modern web and mobile applications.
- User Profile Information: Returns user information in a structured format (JSON Web Token – JWT) for easy consumption by client applications.
- Extensibility: Supports extensions and custom claims to accommodate specific application needs.
How OpenID Connect Works:
- The client application redirects the user to the Authorization Server for authentication.
- The user authenticates with the Authorization Server.
- The Authorization Server redirects the user back to the client application with an authorization code.
- The client application exchanges the authorization code for an ID Token and an Access Token.
- The ID Token contains information about the user’s identity. The Access Token can be used to access protected resources on behalf of the user.
SAML vs. OpenID Connect: Key Differences in Authentication Protocols
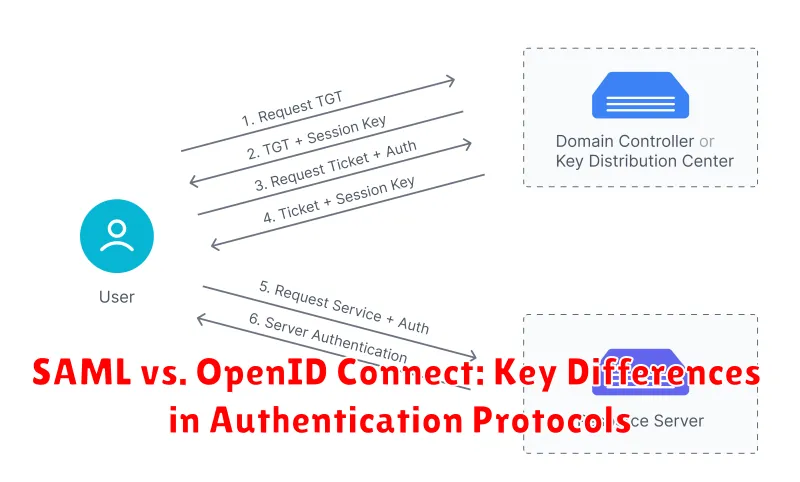
SAML (Security Assertion Markup Language) and OpenID Connect (OIDC) serve the same fundamental purpose: authentication. However, they achieve this through distinct mechanisms. SAML is an XML-based protocol, primarily used for single sign-on (SSO) in enterprise environments. It transfers user identity information via XML assertions between an Identity Provider (IdP) and a Service Provider (SP).
OpenID Connect, on the other hand, is built on top of the OAuth 2.0 authorization framework. It focuses on authentication and provides identity information in the form of JSON Web Tokens (JWTs). OIDC is more developer-friendly and is widely adopted for web and mobile applications.
Here’s a concise comparison:
- Data Format: SAML uses XML, OIDC uses JSON.
- Base Protocol: SAML is a standalone protocol, OIDC is built on OAuth 2.0.
- Complexity: SAML is often considered more complex to implement than OIDC.
- Primary Use Case: SAML is geared towards enterprise SSO, OIDC is preferred for web and mobile apps.
Security Implications: Comparing the Security Strengths of SAML and OpenID Connect
Both SAML and OpenID Connect offer robust security frameworks, but their approaches differ. SAML’s reliance on XML and digital signatures provides strong authentication security, especially against tampering. However, its complexity can lead to configuration errors, potentially creating vulnerabilities.
OpenID Connect, built on OAuth 2.0, benefits from the security features of OAuth. It emphasizes token-based authentication, offering better protection against replay attacks and phishing. Its simpler structure also reduces the risk of misconfiguration.
A crucial difference lies in session management. SAML often utilizes browser cookies, which can be susceptible to Cross-Site Scripting (XSS) attacks if not properly secured. OpenID Connect, with its use of short-lived tokens, typically offers better protection against session hijacking.
Ultimately, the “more secure” protocol depends on the specific implementation and the threat model. Proper configuration, adherence to security best practices, and regular security audits are vital for both.
Use Cases for SAML: When is SAML the Right Choice?
SAML (Security Assertion Markup Language) is particularly well-suited for enterprise environments requiring robust security and compliance.
Here are some key scenarios where SAML excels:
- Enterprise Single Sign-On (SSO): SAML’s mature infrastructure and strong support make it ideal for providing SSO across various internal applications and services.
- Federated Identity Management: When organizations need to securely share user identity information with trusted partners, SAML’s standardized protocol facilitates seamless and secure data exchange.
- Compliance Requirements: Industries with strict regulatory compliance, such as finance and healthcare, often favor SAML due to its comprehensive security features and auditability.
- Legacy Systems Integration: Many older systems and applications are built with SAML support, making it a practical choice for integrating them into modern identity management solutions.
In essence, SAML is a reliable and proven technology for organizations prioritizing security, compliance, and seamless SSO experiences within a controlled, enterprise setting.
Use Cases for OpenID Connect: When is OpenID Connect the Right Choice?
OpenID Connect (OIDC) excels in scenarios where simplicity and user-centric authentication are paramount. It’s particularly well-suited for:
- Mobile Applications: OIDC’s lightweight nature makes it ideal for mobile environments, offering easier implementation and better performance compared to SAML.
- Single Sign-On (SSO) Across Web and Mobile: OIDC facilitates seamless SSO experiences across various applications, including web and mobile, leveraging standardized protocols like OAuth 2.0.
- Consumer-Facing Applications: Given its emphasis on user consent and information sharing, OIDC is well-suited for applications that require access to user profile information, such as social media platforms or e-commerce sites.
- API Security: OpenID Connect is naturally suited for securing APIs, providing a standardized method for verifying the identity of the client application making the API request.
In essence, if your application prioritizes a smooth user experience, ease of integration, and accessing user profile data with consent, OpenID Connect is often the preferred choice over SAML.
Implementation Considerations: Which Protocol is Easier to Implement?
The ease of implementation between SAML and OpenID Connect often depends on the existing infrastructure and the specific requirements of the application.
SAML, while mature and widely supported, can be more complex to implement. Its XML-based structure and intricate configuration requirements can present a steeper learning curve. However, its extensive documentation and established tools can aid in the process.
OpenID Connect, built on top of OAuth 2.0, is generally considered easier to implement, especially for modern web and mobile applications. Its JSON-based communication and simplified flows make it more developer-friendly. Libraries and frameworks for OpenID Connect are readily available, further streamlining the implementation process.
Ultimately, the choice depends on the development team’s familiarity with each protocol and the specific needs of the application. Both have robust tools and libraries, but OpenID Connect often provides a smoother and faster implementation experience, particularly in greenfield projects.
Performance Comparison: SAML vs. OpenID Connect in Terms of Speed and Efficiency
When evaluating SAML and OpenID Connect, performance is a crucial factor. SAML typically involves larger XML payloads, which can lead to increased processing time and bandwidth consumption. This is especially noticeable in environments with limited resources or high transaction volumes.
Conversely, OpenID Connect leverages JSON, a lighter-weight data format. This results in faster processing speeds and reduced bandwidth usage. The use of RESTful APIs in OpenID Connect also contributes to its efficiency. Therefore, OpenID Connect generally exhibits better performance, particularly in mobile and web-based applications where speed is paramount.
However, actual performance can vary depending on the specific implementation, network conditions, and server capabilities. Optimizations such as caching and efficient data compression can mitigate some of the performance differences. Ultimately, a thorough performance test tailored to the specific use case is recommended.
Future Trends in Authentication: What’s Next for SAML and OpenID Connect
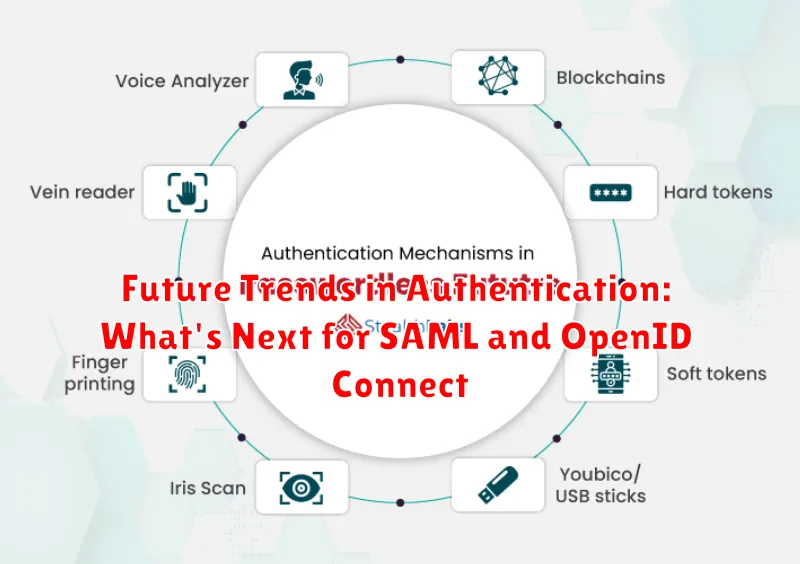
The landscape of authentication is continually evolving, and both SAML and OpenID Connect are adapting to meet new security challenges and user demands. Several key trends are shaping their future.
One significant trend is the increasing adoption of passwordless authentication methods. Both protocols are being enhanced to support techniques like biometric authentication and FIDO2, reducing reliance on traditional passwords and improving security.
Another trend is the growing importance of decentralized identity. Technologies like blockchain are being explored to create self-sovereign identities, potentially integrating with SAML and OpenID Connect to offer users greater control over their personal data.
Finally, the rise of zero-trust security models is driving the need for more granular access control. Future iterations of these protocols will likely focus on enhanced context-aware authentication, allowing for more dynamic and adaptive security policies based on user behavior and device posture.
Choosing the Right Authentication Protocol: A Decision-Making Guide
Selecting the appropriate authentication protocol is crucial for securing your applications. Both SAML and OpenID Connect offer robust solutions, but their strengths lie in different areas. Consider these factors when making your decision:
- Security Requirements: Assess your application’s sensitivity and compliance needs. Does it require highly secure attribute exchange?
- Application Type: Is your application primarily web-based or mobile-first? OpenID Connect is generally favored for mobile and API-driven applications.
- Existing Infrastructure: Does your organization already have a SAML-based identity provider? Leveraging existing infrastructure can reduce implementation complexity.
- User Experience: OpenID Connect often provides a smoother user experience, especially for social login scenarios.
- Federation Needs: If your application needs to integrate with a large number of external services, OpenID Connect may offer simpler federation capabilities.
By carefully evaluating these considerations, you can determine whether SAML or OpenID Connect is the better fit for your specific needs, ultimately enhancing the security and usability of your application.

