In today’s digital landscape, data security and trust are paramount. For businesses handling sensitive customer information, achieving SOC 2 compliance is not just a checkbox; it’s a critical investment in safeguarding data and building confidence with clients. But what exactly *is* SOC 2, and why should your organization prioritize achieving this standard? This article will demystify SOC 2 compliance, explaining its core principles and outlining its significance for businesses of all sizes across various industries.
SOC 2 (System and Organization Controls 2) is an auditing procedure that ensures your service providers securely manage your data to protect the interests of your organization and the privacy of its clients. This report, developed by the American Institute of Certified Public Accountants (AICPA), focuses on five “Trust Services Criteria“: security, availability, processing integrity, confidentiality, and privacy. Understanding these criteria and how they apply to your business is the first step in navigating the SOC 2 compliance journey, which ultimately strengthens your security posture and enhances your reputation in the marketplace.
What is SOC 2 Compliance? A Comprehensive Overview
SOC 2 (System and Organization Controls 2) is a widely recognized auditing procedure designed to ensure service providers securely manage data to protect the interests of their organization and the privacy of its clients. Developed by the American Institute of Certified Public Accountants (AICPA), a SOC 2 report demonstrates an organization’s ability to meet industry standards and best practices regarding data security.
Specifically, SOC 2 compliance validates a service organization’s controls relevant to security, availability, processing integrity, confidentiality, and privacy of user data. These are known as the Trust Services Criteria. A successful SOC 2 audit provides assurance to clients and stakeholders that the organization maintains a robust security posture.
Unlike other compliance frameworks, SOC 2 is unique in that it is not mandated by law. Instead, it is a voluntary compliance standard that businesses pursue to demonstrate their commitment to data security. Increasingly, businesses are requiring their vendors to be SOC 2 compliant as a condition of doing business.
The Five Trust Services Criteria: Understanding the Core Principles of SOC 2
SOC 2 compliance revolves around the Trust Services Criteria (TSC), a set of standards established by the American Institute of Certified Public Accountants (AICPA). These criteria are the benchmarks against which a service organization’s controls are evaluated.
The five TSC are:
- Security: Protecting information and systems from unauthorized access, use, or disclosure.
- Availability: Ensuring the system is available for operation and use as agreed upon.
- Processing Integrity: Ensuring system processing is complete, valid, accurate, timely, and authorized.
- Confidentiality: Protecting information designated as confidential.
- Privacy: Handling personal information in conformity with the entity’s privacy notice and the AICPA’s generally accepted privacy principles (GAPP).
An organization must demonstrate adherence to the security criteria and then select one or more of the remaining criteria based on the services they provide and commitments they make to their clients. Understanding these criteria is crucial for organizations seeking SOC 2 compliance.
Why is SOC 2 Compliance Important for Businesses?

SOC 2 compliance is crucial for businesses that handle sensitive customer data in the cloud. It demonstrates a commitment to data security and privacy, building trust with clients and partners.
Here’s why it matters:
- Competitive Advantage: SOC 2 certification can differentiate your business from competitors, especially when bidding for contracts that require stringent security measures.
- Enhanced Trust and Reputation: It assures customers that their data is handled securely and responsibly, enhancing your brand reputation.
- Risk Mitigation: SOC 2 compliance helps identify and mitigate potential security risks, reducing the likelihood of data breaches and associated financial losses.
- Meeting Regulatory Requirements: It can help meet the security expectations outlined by various data privacy regulations.
- Business Growth: By establishing strong security controls, businesses can scale operations with confidence.
In essence, SOC 2 compliance is an investment in your company’s long-term security, reputation, and growth.
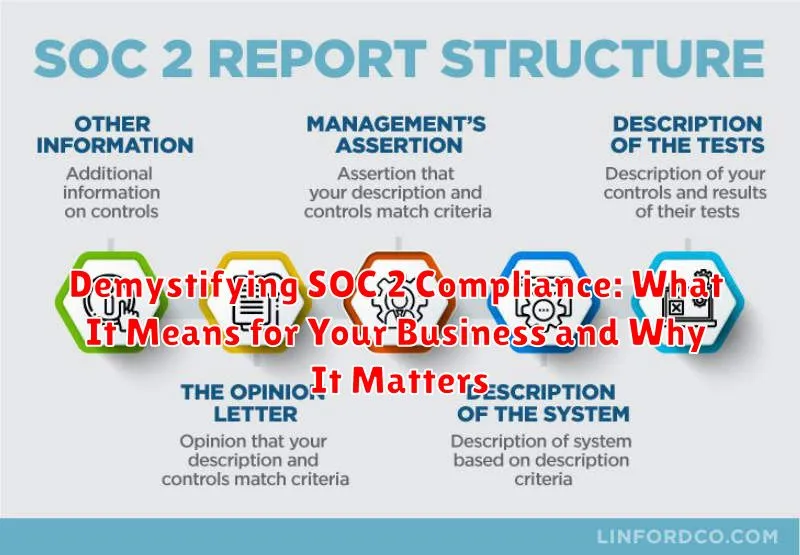
Types of SOC 2 Reports: Type I vs. Type II
SOC 2 reports come in two types, each offering a different level of assurance regarding a service organization’s controls. Understanding the distinction between Type I and Type II reports is crucial for businesses seeking to assess their vendors’ security posture.
Type I Report
A Type I report focuses on the design of controls at a specific point in time. It attests to whether the service organization’s description of its system is fairly presented and whether the controls are suitably designed to achieve the related control objectives. In essence, it’s a snapshot view of the controls’ design effectiveness.
Type II Report
A Type II report goes a step further by examining the operating effectiveness of controls over a specified period, typically six months to a year. This report assesses whether the controls, as designed, were operating effectively throughout the period. A Type II report provides a more comprehensive and robust assurance compared to a Type I report because it considers the actual implementation and performance of the controls over time.
Therefore, businesses typically prefer Type II reports when evaluating the security and compliance of their service providers, as they provide a more in-depth assessment of control effectiveness.
Who Needs SOC 2 Compliance?
SOC 2 compliance is primarily relevant for service organizations that store customer data in the cloud. This includes a broad range of companies, but is especially critical for:
- Software as a Service (SaaS) providers: These companies manage substantial amounts of client data.
- Cloud computing vendors: Similar to SaaS providers, these vendors need to prove their security.
- Data centers: Entities that host and manage data require strong security controls.
- Any business that processes or stores customer data in the cloud: Even if not primarily a tech company, handling sensitive data necessitates SOC 2.
Essentially, if your organization provides a service where you handle sensitive customer information in the cloud, then you most likely need SOC 2 compliance. Customers are increasingly demanding SOC 2 reports as a condition of doing business, ensuring their data is secure. Failing to obtain SOC 2 compliance can result in lost business opportunities and reputational damage.
The SOC 2 Compliance Process: A Step-by-Step Guide
Achieving SOC 2 compliance involves a structured process to ensure your organization meets the required standards. Here’s a step-by-step guide:
- Gap Assessment: Identify areas where your current security practices fall short of SOC 2 requirements.
- Remediation: Implement necessary changes to address the identified gaps, such as updating security policies, improving access controls, and enhancing monitoring systems.
- Documentation: Document all relevant policies, procedures, and controls. This documentation will be crucial during the audit.
- Implementation: Put the documented policies and procedures into practice across your organization.
- SOC 2 Audit: Engage a qualified auditor to assess your compliance with the Trust Services Criteria. This involves providing evidence and undergoing testing.
- Report Generation: The auditor will issue a SOC 2 report outlining their findings, including any exceptions or areas for improvement.
- Continuous Monitoring: Regularly monitor your controls and processes to maintain compliance and address any emerging risks.
Benefits of Achieving SOC 2 Compliance
Achieving SOC 2 compliance provides numerous advantages for businesses, enhancing their reputation and operational efficiency. Gaining customer trust is paramount. SOC 2 certification demonstrates a commitment to data security, reassuring clients that their information is handled responsibly. This can lead to increased customer acquisition and retention.
Furthermore, SOC 2 compliance often becomes a competitive differentiator. Many enterprises require their vendors to be SOC 2 compliant, making it a necessity for securing contracts. Internally, the process of achieving and maintaining compliance drives improvements in data security practices and operational controls. It fosters a culture of security awareness within the organization, reducing the risk of data breaches and other security incidents.
In summary, the benefits extend beyond simply passing an audit; they encompass stronger customer relationships, improved security posture, and a competitive edge in the marketplace.
Challenges in Achieving and Maintaining SOC 2 Compliance
Achieving and maintaining SOC 2 compliance can present several challenges for organizations. One significant hurdle is the initial assessment and gap analysis, which requires a thorough understanding of the organization’s existing security controls and alignment with the Trust Services Criteria (TSC). Identifying and remediating gaps can be time-consuming and resource-intensive.
Another challenge lies in the ongoing monitoring and documentation of controls. SOC 2 requires continuous monitoring to ensure the effectiveness of security measures. Maintaining accurate and up-to-date documentation of policies, procedures, and system configurations is crucial for demonstrating compliance during audits. This can be especially difficult for organizations with complex IT environments.
Furthermore, employee training and awareness are essential for SOC 2 compliance. Ensuring that all employees understand their roles and responsibilities in maintaining security is vital. Regular training sessions and security awareness programs are necessary to mitigate the risk of human error or negligence.
Finally, the cost of SOC 2 compliance can be a significant barrier for some organizations. The cost of audits, remediation efforts, and ongoing maintenance can strain budgets, particularly for smaller businesses. Careful planning and budgeting are essential to ensure a successful SOC 2 compliance journey.
SOC 2 Compliance Costs: What to Expect
Achieving SOC 2 compliance involves several cost factors that businesses should consider. These costs can vary significantly depending on the size and complexity of the organization, the scope of the audit, and the readiness of existing controls.
Key cost components include:
- Gap Assessment: Evaluating current practices against SOC 2 requirements.
- Remediation: Implementing or enhancing controls to address identified gaps.
- Audit Fees: Payments to a certified public accountant (CPA) firm for conducting the audit.
- Software and Tools: Investment in security tools or compliance management platforms.
- Internal Resources: Time spent by internal staff on the compliance effort.
- Consulting Fees: Engaging external consultants for guidance and support.
It’s essential to obtain quotes from multiple CPA firms and carefully assess the scope of work to understand the expected investment. Proper planning and preparation can help minimize costs and ensure a smooth compliance process.
How to Prepare for a SOC 2 Audit?
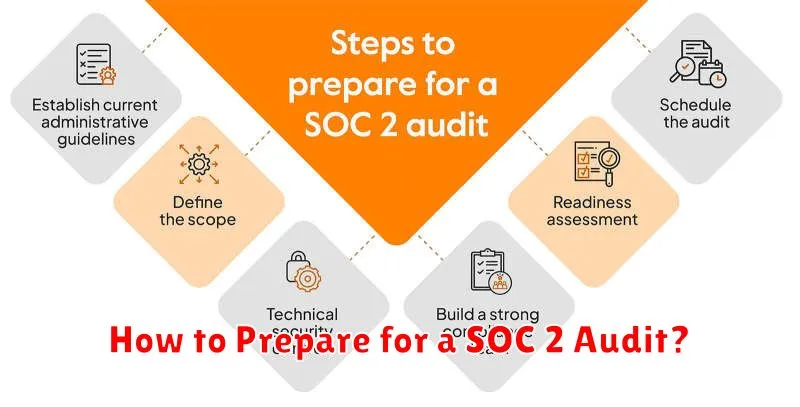
Preparing for a SOC 2 audit is crucial for a successful outcome. A well-prepared organization demonstrates its commitment to data security and increases the efficiency of the audit process.
Here are key steps to consider:
- Define the Scope: Clearly identify the systems and data that fall within the scope of the audit.
- Gap Analysis: Conduct a thorough gap analysis to identify areas where your organization’s controls do not meet the Trust Services Criteria.
- Remediation: Implement necessary changes to address identified gaps. This may involve updating policies, implementing new security controls, or improving existing processes.
- Documentation: Maintain comprehensive documentation of all relevant policies, procedures, and controls. Accurate and up-to-date documentation is essential for demonstrating compliance.
- Employee Training: Ensure all employees are aware of and trained on relevant security policies and procedures.
- Pre-Audit Assessment: Consider conducting a pre-audit assessment to identify and address any remaining weaknesses before the official audit.
By taking these proactive steps, your organization can significantly improve its chances of a successful SOC 2 audit.